As a Cybersecurity Analyst, staying ahead of the ever-evolving threat landscape is a non-negotiable part of the job. But in a fast-paced environment, manually looking through multiple sources for the latest cybersecurity news can be inefficient and unsustainable. That’s what sparked the idea for the “Threat Intel Automation” project: an initiative to automate the entire process of gathering, summarizing, and delivering daily cybersecurity updates to our team via Slack and Gmail. As a SIEM (Security Information and Event Management) tool-based team, the detection team requires updates on the latest CVEs and cybersecurity news, and this project ensures to:
- Deliver a 5–10 minute cybersecurity bulletin to enhance team-wide awareness and security education by explaining one new attack campaign and CVEs daily.
- Keep focus on how the attack campaign unfolds step-by-step, identifying attacker methods.
- Track evolving threat methodologies and continuously document the procedures to build a comprehensive understanding across the team.
The Launch: Automating with n8n
The first step was identifying a tool that could handle complex workflow automation without building from scratch. I chose n8n, an automation platform known for its versatility and ease of use. It offered just the right balance between a user-friendly interface and deep customization, allowing me to quickly start designing a workflow without writing endless lines of code.
The core idea was to create a daily routine that fetches the latest cybersecurity news, filters it, summarizes it, and then delivers it straight to our team.
Building the Threat Intel Pipeline
I started the threat intel automation project by sourcing RSS feeds from top cybersecurity news platforms, including The Hacker News, BleepingComputer, unit42 (part of Palo Alto), Splunk, and ThreatPost. Why these sources? These sources provide the latest and most relevant cybersecurity news, which includes a proper mixture of technical and general cybersecurity topics. I configured n8n to pull these feeds and merge them into a unified stream of daily news.
Next came the challenge of sorting and selecting relevant updates. I built logic into the workflow to filter duplicates and old news, ensuring that only fresh, high-impact cybersecurity news was delivered. This task took some effort to create a few test workflows and try out multiple scenarios, which gave the results as per the requirements.
Once the filtering was in place, the articles were passed through OpenAI’s chat model for summarization. This AI-powered summarization was a game-changer; instead of bombarding the team with full-length articles, we now had clear, concise, and context-rich summaries, making it easier for everyone, technical or not, to stay informed. Finally, the summarized output was sent directly to Slack and user Gmail accounts, keeping threat intelligence both timely and accessible.
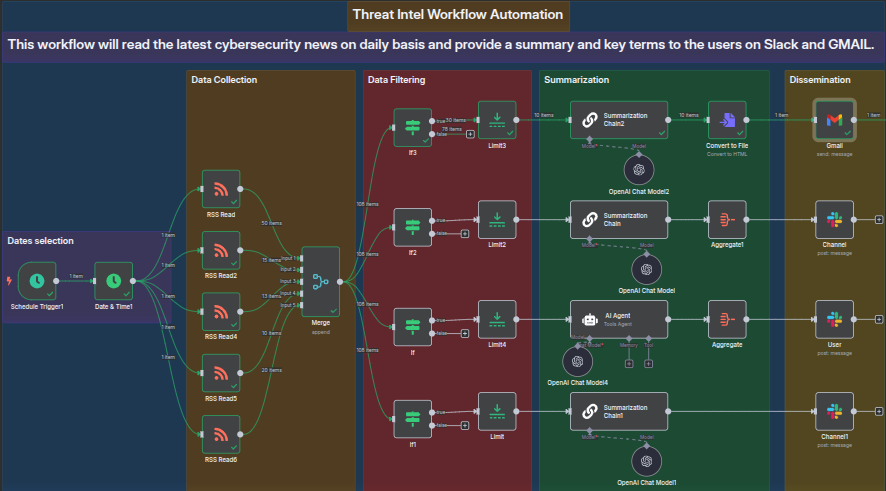
Threat Intel Workflow (automated with n8n)
This project deepened my understanding of automation tools, workflow logic, and third-party API integration. More importantly, it taught me how to approach problems from a productivity and usability perspective, how to turn a repetitive task into a fully automated, value-driven process. I also got firsthand experience in working with AI-powered tools for summarization, learning how to prompt effectively and control the output for clarity and relevance.
The Threat Intel Automation project wasn’t just about building a workflow; it was about empowering the team with timely, relevant information in a format they could actually use. In a world where time and clarity are everything, automating threat intel delivery has proven to be a small investment with massive returns. This journey not only boosted our operational efficiency but also strengthened our collective situational awareness, something every cybersecurity team can benefit from. For other verticals and teams in the organization, a daily 15-minute briefing of this summarized news in the form of a podcast helped us to enhance organization-wide awareness as well.